Forays into Security Testing with Bugcrowd and Twilio

Until recently I had heard of security flaw finding competitions and websites and assumed they were only for the hacker elite. As someone who spends his days creating software I’d not really looked in to them, thinking that I wouldn’t be able to find anything that hadn’t been found before.
However thanks to a bit of serendipity and some great people working on support I managed to report a security vulnerability and earn myself some money through a website called Bugcrowd as well as getting an extra bonus for finding the issue during OWASP Bug Week 2014.
Earlier in 2014 I ran a HackDay for Fivium, the company I work for. As part of that I created a voting system where everyone could vote for their favourite projects via text message, using my favourite API: Twilio.
When I wrote the voting system I made sure to sanitise the text message input so that my website was safe from XSS attacks. Though Fivium isn’t a security company it has its fair share of devious developers, and I know the best developers like nothing more than to poke and prod every system they can lay their fingers on. Thankfully during the event my XSS protection worked, as demonstrated when someone in the crowd submitted a vote for “<script>alert(1);</script>”. In my voting system it came out safely escaped and a few laughs were had at the attempt.

A few months later I got an email from Twilio letting me know the credit on my account was running low. I haven’t used the API much since the HackDay so I logged in to Twilio to find out why my balance was running low. Thankfully Twilio keeps a log of all the messages and calls in and out of the numbers associated with your account so I could easily see how my credit was starting to dip.
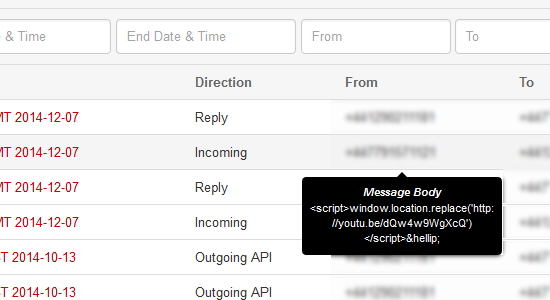
I also got a very odd alert message popping up when I rolled over one of the entries in the text message log, a HTML alert saying “1”…
I immediately recognised that this was a stored XSS problem and contacted Twilio support. I spotted this at 8pm on a Sunday night however, so I didn’t expect a response for a few days, but within half an hour a reply came. The person working support asked if I could reproduce the issue and to provide some extra information to pass on to their developers and security team to check out. After a little back and forth, and constructing a new message that would rickroll anyone checking my text message history I left it with them, just hoping it would get fixed and I’d perhaps get a thumbs up that it was good to go.
The next day I got a reply from them letting me know that the security team had checked out my test case and I should report it on their Bugcrowd page to potentially get “rewarded”.
After signing up I was met with a fairly daunting submission form that was obviously aimed at professional security testers. As I didn’t use any tools or link a series of small exploits together I filled in the submission with jokes where I didn’t have anything to put.
A few days after submitting I got an email letting me know I’d gotten a decent sized monetary reward however, which is far more than I’d expected to get initially! Especially for what was just a text message sent to exploit my own system originally and a few minutes talking to support and making a test case.

A week or so later I got a message from one of the Bugcrowd staff asking if they could publicly credit my for my submission. When I created my account on Bugcrowd I had made it private as I figured I didn’t fit in with the other security pro’s, but she wanted to mention my account name and my vulnerability report in an upcoming blog post.
The blog post was about the OWASP Bug Week that Bugcrowd run where they partner with Open Web Application Security Project (OWASP) and have a competition over a week to find the “Best Bug” and to encourage the community to innovate and improve application security.
While I hadn’t won the competition I did get an Honourable Mention for the silly reproduction steps I’d put in my submission as I had no idea how to use the vulnerability to do anything too nefarious. They also liked that the tools I’d used were a phone and my fingers, as I assume those aren’t the typically tools of the trade when doing security testing!
To wrap up, thank you to Twilio for having great support and a security team who pointed me towards Bugcrowd. And thanks to Bugcrowd for accepting and even mentioning my vulnerability submission in a blog post. Here’s to future bug hunting!
